As we traverse the challenges of online gaming, comprehending how Avia Fly 2 prioritizes player data protection is essential. With the rising concerns regarding data privacy, it’s necessary to review the measures in place that align with UK’s GDPR and Data Protection Act. Let’s investigate the cutting-edge technologies and protocols that ensure our information stays secure in this online environment, shaping a protected gaming experience for us all. What elements are notable in this initiative?
Key Takeaways
- Avia Fly 2 conforms with UK GDPR and Data Protection Act 2018, ensuring strict standards on consent and data handling for player privacy.
- Advanced security technologies like quantum encryption and blockchain are utilized to secure player data from cyber threats and guarantee transaction integrity.
- Multi-factor authentication and secure password policies enhance user verification, while continuous monitoring detects potential threats in advance.
- Players are provided with education on strong password practices and phishing recognition, promoting awareness of personal data safety in gaming.
- Transparent communication about data protection efforts establishes trust, with open channels for feedback and regular updates on security measures.
Understanding Data Privacy Regulations in the UK
As we traverse the complexities of data privacy regulations in the UK, it’s essential to acknowledge the system established by the UK General Data Protection Regulation (UK GDPR) and the Data Protection Act 2018. These frameworks define our data rights, permitting individuals to control their personal information. We’re responsible with fostering privacy awareness and ensuring compliance when managing user data.
Both legislations mandate strict guidelines on gaining consent, data processing, and entitlements to access or delete personal data. It’s essential for us to stay knowledgeable about these obligations, as they affect our practices in data protection. By emphasizing transparency, we not only comply with the law but also foster trust with players, creating a more secure gaming environment that honors their privacy.
Advanced Encryption Technologies Used by Avia Fly 2
In investigating the advanced encryption technologies employed by Avia Fly 2, we can review the sophisticated data encryption techniques that safeguard player information. Additionally, robust user authentication systems play a essential role in ensuring that access to personal data remains tightly controlled. Together, these steps demonstrate a solid commitment to protecting player privacy in our game.
Advanced Data Encryption Methods
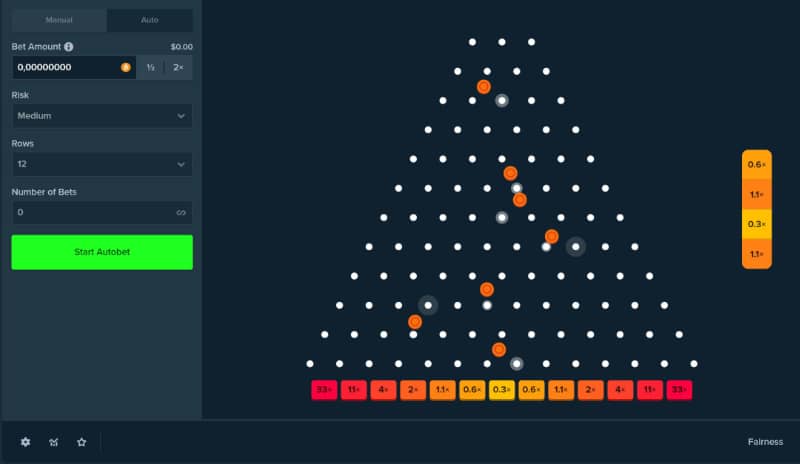
While the demand for effective data protection has never been more important, Avia Fly 2 employs sophisticated encryption approaches to ensure player information stays safe. We utilize quantum encryption, which utilizes the laws of quantum mechanics to generate secure codes, guaranteeing that even the most sophisticated cyber threats are neutralized. Additionally, we incorporate blockchain security to keep an immutable ledger of transactions and user data, offering an additional layer of trust and transparency. This distributed approach not only bolsters data integrity but also minimizes the risks associated with single-point data storage. By integrating quantum encryption with blockchain technology, we’re setting a new level for player data protection, ensuring players can enjoy Avia Fly 2 with confidence.
Secure User Authentication Protocols
Recognizing the need for solid user authentication, we’ve carried out cutting-edge protocols in Avia Fly 2 that use state-of-the-art encryption technologies. Our commitment to player data security is apparent through the following measures:
- Biometric Authentication
- Token-Based Access
- Multi-Factor Authentication
- End-to-End Encryption
These protocols not only strengthen our security structure but also inspire confidence in our players, ensuring them that their sensitive data is well protected while they experience Avia Fly 2.
Robust Authentication Processes for Player Safety
In our examination of solid authentication processes for player safety, we must take into account the critical roles of multi-factor authentication and secure password policies. By putting these measures into action, we greatly enhance the defense against illicit access. Additionally, routine security audits assure that our systems remain robust and flexible to developing threats.
Multi-Factor Authentication

As we examine the intricacies of securing player data in Avia Fly 2, it becomes apparent that implementing multi-factor authentication (MFA) is vital for enhancing player safety. This strong authentication process not only fortifies user verification but also strengthens identity protection against unapproved access.
- MFA merges two or more verification methods.
- Players can utilize biometrics, SMS codes, or authenticator apps.
Secure Password Policies
While many believe that multi-factor authentication is sufficient on its own, establishing secure password policies is similarly important for safeguarding player accounts in Avia Fly 2. We must emphasize password complexity, insisting players to choose passwords that include uppercase and lowercase letters, numbers, and special characters. This diverse composition significantly improves security, making it more difficult for unpermitted users to achieve access. Additionally, user training is imperative; informing our players on the significance of consistently updating passwords and detecting phishing attempts nurtures a culture of security awareness. By executing these strong password policies, we’re diligently reducing the risk of breaches and assuring that our players can concentrate on experiencing the game without fearing about their personal data.
Regular Security Audits
Creating secure password policies is a basic step, but it doesn’t conclude there; regular security audits are paramount in ensuring effective authentication processes that protect player safety. These audits allow us to conduct thorough risk assessments and enhance our vulnerability management, ensuring the highest safety standards for our players.
- Find potential security vulnerabilities across our systems.
- Examine the effectiveness of current authentication methods.
- Create detailed reports for constant improvement.
- Ascertain compliance with field regulations and standards.
Continuous Monitoring and Threat Detection
In the domain of game security, continuous monitoring and threat detection are crucial components that safeguard player data from new risks. We execute real-time analytics to incessantly assess gameplay data, identifying potential vulnerabilities as they emerge. This preventive approach allows us to stay one step ahead of threats, guaranteeing player information remains secure. Automated alerts play a pivotal role in our security strategy, alerting us immediately when suspicious activities are identified. By leveraging these technologies, we create a solid defense that not only reacts to but foresees potential security breaches. Our commitment to ongoing improvement ensures that our protective measures evolve alongside new threats, ultimately cultivating a safe gaming environment for all players.
Player Education: Promoting Safe Gaming Practices
To guarantee a secure gaming experience, we must emphasize player education in promoting safe gaming practices. By cultivating gaming awareness, we enhance player safety and guarantee everyone enjoys a secure environment. Here are key practices we should recommend:
- Use secure, unique passwords and turn on two-factor authentication.
- Be wary about sharing personal information, even within the game.
- Frequently update software and apps to protect against vulnerabilities.
- Spot phishing attempts and suspicious links to avoid data breaches.
Compliance With GDPR and Data Protection Laws
As we emphasize player education in responsible gaming practices, it’s vital to recognize our responsibilities regarding compliance with GDPR and other data protection laws. We recognize that data privacy isn’t just a regulatory requirement; it’s essential to our players’ trust. Our pledge to legal compliance protects that all player data is processed legally, clearly, and securely. We’ve put in place strict policies to protect personal information and to give players total control over their data. Routine audits and compliance assessments confirm that our practices comply with evolving regulations. Additionally, we educate our team on data handling protocols to stop breaches and unauthorized access, reinforcing our commitment to maintaining the top standards of data protection.
Building Trust Through Transparency and Communication
Trust grows through transparency and open communication in the gaming community. At Avia Fly 2, we understand that building this trust is essential for player assurance and loyalty. Here are some transparency benefits we accept:
- Routine updates on data protection practices
- Open channels for player input and inquiries
- Clear articulation of our privacy policies
- Public disclosure on security measures taken
Our communication strategies ensure that players feel aware and secure, bolstering our commitment to data protection. By disclosing our practices and inviting dialogue, we foster an environment where players know their data is honored and safeguarded. This forward-thinking approach not only elevates trust but also fortifies our relationship with the gaming community, in the end improving the overall player experience.
Frequently Asked Questions
How Does Avia Fly 2 Handle User Data Breaches?
When addressing data breaches, we guarantee immediate response through predefined protocols. By executing rigorous player privacy measures, we react promptly to safeguard user information, reinforcing our commitment to upholding trust and security within the gaming community.
Can Players Delete Their Account and Data Permanently?
Certainly, players can request account deletion, ensuring data privacy is upheld. Once we initiate this process, all personal data will be completely removed, aligning with our commitment to safeguarding user information and respecting individual choice.
What Information Is Collected During Gameplay?
During gameplay, we collect data for gameplay analytics, including player preferences and performance metrics, ensuring player privacy is prioritized. This information helps us improve game quality while safeguarding our players’ personal data efficiently.
Are Player Data Shared With Third Parties?
We’re committed to data privacy and don’t share player data with third parties. Our policies align with rigorous guidelines, ensuring transparency and protecting your information from unauthorized access while elevating your gaming experience.
How Often Is Player Data Backed Up?
We regularly assess our data frequency in backup processes, ensuring player data’s integrity. Typically, backups occur on a daily basis, allowing us to quickly recover information and maintain strong security, safeguarding our community’s experience and privacy effectively.

Estudié comunicación mas el deseo de escribir me viene, sobre todo, de las
ganas de escuchar con profundidad a las personas.
Me pongo lentes diversos para comprender lo que cada uno me cuenta, desde su
propio punto de vista. Soy toda oídos.
Mi desafío es materializar la necesidad de cada cliente en textos persuasivos y
creativos. Acompañar para descubrir el brillo propio de cada proyecto.
Practique mucho, entrené el músculo de la escritura. Hoy me siento segura
para expresar claramente mis ideas y también las de los demás.
Elegir con dedicación esas pocas y voluminosas palabras que te hagan sentir
sí, eso es lo que quería decir.
“Te escucho 100%. Me adapto a tu necesidad y a tu público. Relataremos historias vívidas porque las ideas atraen
pero las experiencias, arrastran.
Nos focalizamos en lo que tenés, no lo que te falta. Esa potencia es siempre el punto de partida. Jamás podré sacarme los anteojos en “4D” que me regaló mi amiga Lala Deheinzelin. Para evaluar los proyectos desde múltiples dimensiones para sumar valor (Con lentes 4D, vemos no solo las riquezas tangibles, como lo ambiental y lo financiero, sino también las intangibles, como lo social y lo cultural).
Soy entusiasta de la potencia de la red. Complementamos para armar equipos de trabajo poderosos”.